Security has become pervasive in the contemporary People's Republic of China. Its logics, technologies and practices shape Chinese politics as they do Chinese society. With the PRC's growing global reach, moreover, its implications are felt beyond China's national borders.
The research consortium Security in China breaks new ground both in the study of Chinese security politics and in critical security studies by bringing together an international group of experts to study the workings and politics of security in different loci of the contemporary PRC. The consortium is a collaboration between the University of Turku and Tampere University and it is funded by the Academy of Finland for the years 2019–2023.
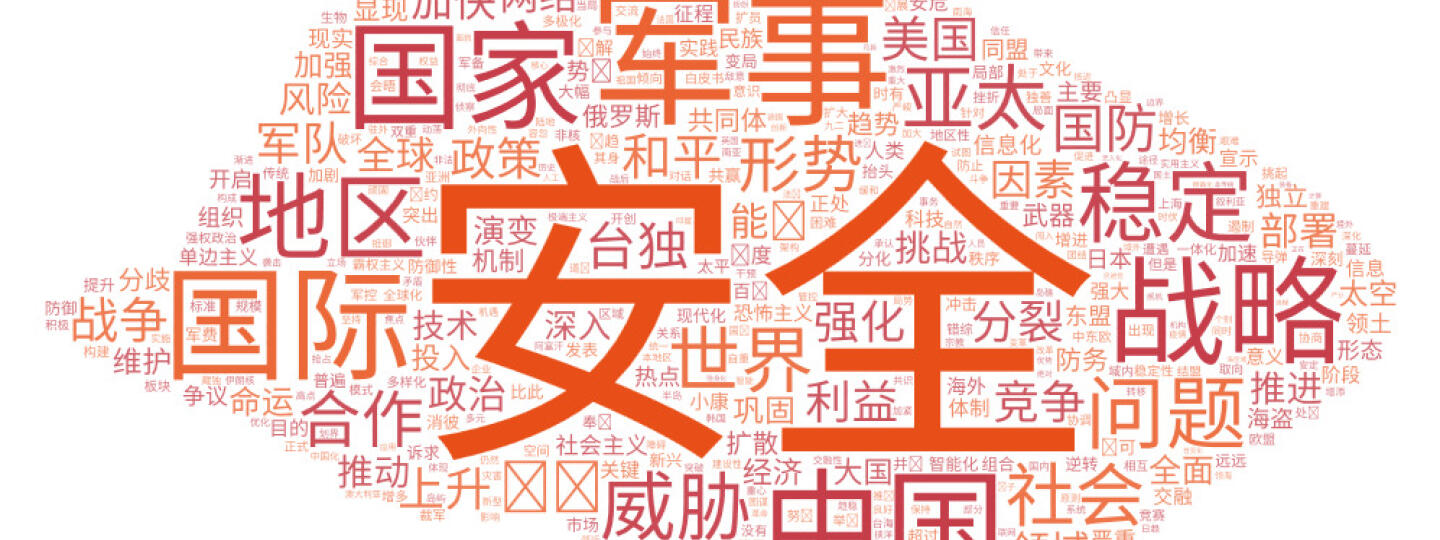
(The word cloud was generated from the Chinese government's white paper "China's National Defense in the New Era" (2019).)
About
The Security in China research consortium studies the workings of security in the People's Republic of China. The issue is timely yet understudied, as much of the academic study of Chinese security politics focuses on military and national security, whilst studies on non-traditional security have avoided China. Moreover, the secretive security machinery of the People's Republic has not alleviated the problem.
Security in China seeks to discern Chinese visions of the political from how it speaks about security, how it tries to turn this speech into reality with the aid of technology, and how it practices security. The consortium's main foci are thus concepts, technologies and practices of security and the socio-political consequences they entail. The overarching problem for the project is: What is the difference between security in Chinese high politics and its everyday implementation? The main problem is then pursued through four core questions:
- How has the concept of security been adopted and how has it evolved in China?
- How do Chinese security actors and practitioners produce security through their speech, technologies and everyday practices?
- Do Chinese understandings, techniques and practices of security, and the vision of the political they entail differ from those prevalent in liberal political orders?
- How should Chinese security understood in this way be taken into account when dealing with China?
These core questions are used to guide the study of the conceptual history of national security in China; investigation of the security logics of online censorship and propagation; and a sociology of Chinese security experts through case studies on control of internal migration, and climate and energy security. Together the lines of inquiry yield knowledge on the politics of non-traditional security in China.
The consortium is led by Professor Juha A. Vuori (Tampere University) and Professor Lauri Paltemaa (CEAS). The project personnel and external collaborators consist of international group of experts at different stages of academic career.
The consortium enjoys the Academy of Finland funding for early career researchers (decision # 323702) for the duration of academic years 2019-2023.
Paltemaa, L., Vuori, J. A., Mattlin, M., & Katajisto, J. (2020). Meta-information censorship and the creation of the Chinanet Bubble. Information, Communication & Society, 1–17. https://doi.org/10.1080/1369118X.2020.1732441
Related publications
Vuori, J. A., & Paltemaa, L. (2019). Chinese Internet Control over Social Media Discourse. In C. Shei (Ed.), The Routledge Handbook of Chinese Discourse Analysis, 391–403. London: Routledge.
Vuori, J. A. (2018). Let’s just say we’d like to avoid any great power entanglements: desecuritization in post-Mao Chinese foreign policy towards major powers. Global Discourse, 8(1), 118-136. https://doi.org/10.1080/23269995.2017.1408279
Vuori, J. A. (2015). Contesting and Resisting Security in Post-Mao China. In T. Balzacq (Ed.), Contesting Security: Strategies and Logics. London: Routledge. https://doi.org/10.4324/9780203079850
Paltemaa, L. & Vuori, J. A. (2015). The Lexicon of Fear: Chinese Internet Control Practice in Sina Weibo Microblog Censorhip. Surveillance & Society, 13(3), 400-421. https://doi.org/10.24908/ss.v13i3/4.5404
Vuori, J. A. (2014). Critical Security and Chinese Politics: The Anti-Falungong Campaign. London: Routledge. https://doi.org/10.4324/9780203718766
Vuori, J. A. (2011). Three Takes on the Counter-Revolutionary: Studying Asymmetrical Political Concepts in the People’s Republic of China. In K. Junge & K. Postoutenko (Eds.), Asymmetrical Concepts After Reinhart Koselleck: Historical Semantics and Beyond, 115–140. Bielefeld: transcript-Verlag.
Vuori, J. A. (2011). Religion bites: Falungong, securitization/ desecuritization in the People’s Republic of China. In T. Balzacq (Ed.), Securitization Theory: How Security Problems Emerge and Dissolve, 186–211. London: Routledge.
Paltemaa, L., & Vuori, J. A. (2009). Regime Transition and the Chinese Politics of Technology - From Mass science to the Controlled Internet. Asian Journal of Political Science, 17(1), 1-23. https://doi.org/10.1080/02185370902767557
Paltemaa, L. (2008). These Bytes Can Bite - Chinese Politics of Technology and the Controlled Internet. In J. Rinne & T. Häyhtiö (Eds.), Net working/Networking – Politics on the Internet, 189-204. Tampere: Tampere University Press.